Phones, Laptops, iPads, or for that matter a lot of different gadgets are a part of our daily routine. With the advancement in technology, we’ve started to heavily rely on their smart and fancy features. Digital voice assistants are the new boom in most tech spheres leading upto dedicated AIs for home automation. Ideally, these assistants are created to make our lives easier, but in the back of our mind we always dreaded that it could spiral out of control any moment. And a team of US and Chinese researchers proved just that!
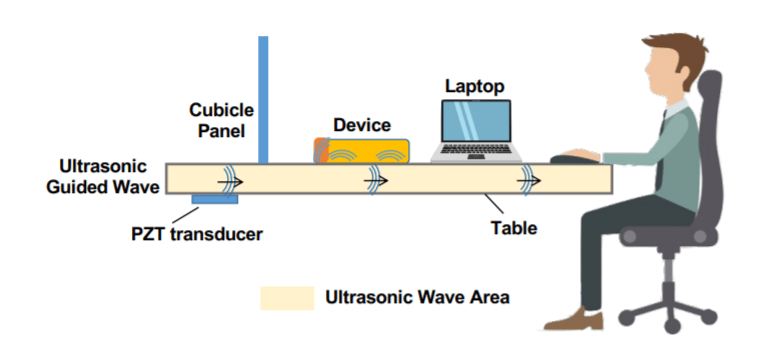
A hack named ‘Surfing Attack’ was recently rolled out where security researchers used ultrasonic guided waves, that is inaudible to the normal human ear. But this wave is able to directly forge a connection and communicate with the device using the Voice Assistant feature.
Previous researches have proved that waves can in fact manipulate with your phone, but that required a very close proximity and any object could interfere and kill the process. But that paved the way for this excellence.
What is an Ultrasonic Wave?
Ultrasonic waves are vibrations of sound waves with frequencies much higher than perceptible to the human ear. They travel through a medium and can usually go above 20,000 Hertz. Few animals are audible to such sounds, while many objects can reflect/ refract the waves.
How Can Ultrasonic Guided Waves Hack Your Phone?
The US and Chinese researchers team who developed this cyber-attack say that this guided wave can communicate, control and command your devices’ microphone to perform a certain set of tasks. This mode doesn’t even require the gadget to be within eye-sight range, and still manages to send signals through solid objects.
“The Experiment”
To test this theory out, researchers Qiben Lin, Kehai Liu, Qin Zhou, Hanqing Guo and Ning Zhang used the simplest technique that all of us are habitual of — placing your phone on a table. They started by preparing an attack device and sticking it underside a metal table top. This remotely controlled device will then send signals through the table to the phone placed above and trigger it with Ultrasonic voice commands. But the most surprising part is yet to unfold — the attack device was an off-the shelf $5 PZT transducer.
These sly operations can consist of:
- Fraud calling
- Reading and retrieving text information in form of messages and emails
- Manipulating AI enabled Home systems
- Lock/ Unlock Cars
- Breach 2-factor authentication by reading the secret codes
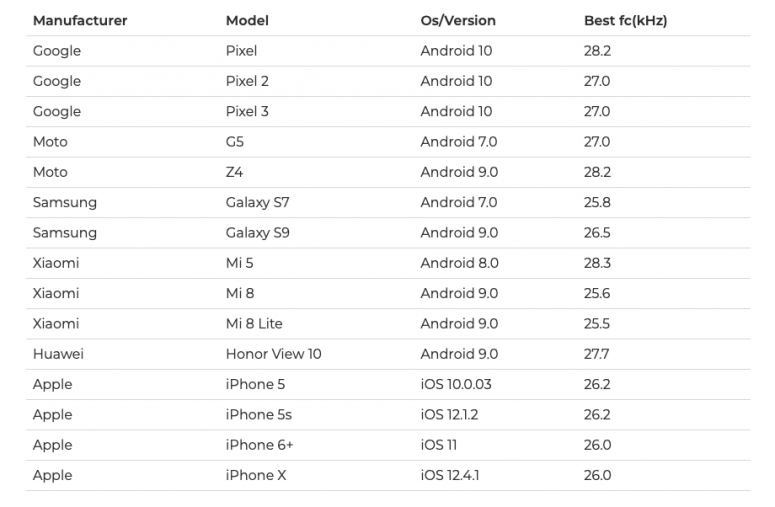
And many more unexplored opportunities. The experiment was carried out and tested on the following phones, including ones with silicone cover cases. The 17 mentioned smartphone models are produced by Apple, Samsung, Google, Motorola, Huawei and Xiaomi:
How to Prevent Ultrasonic Wave Attacks on your Phones & AI Devices?
Since this brilliant team carried out an extensive research program, they would of course be generous enough to recommend some necessary preventive methods. So, read on for a list of Do’s and Don'ts to follow in your everyday routine, so no hacker can hack his way inside your personal life:
- Avoid placing your phone directly on a surface, or at least reduce the touching area
- Look out for any usual activity on your phone, specially when left unattended
- A clothing barrier like woven mat can help in avoiding such transmissions
- Rather than silicon, use thick cover cases or maybe wood
- For phone unlock, disable voice match or similar features. Prefer patterns or passcodes
- Always lock your device before placing down, and make sure to disable Voice Assistant on Lock screen
If you want to dive in much deeper, we suggest you to read this official White Paper, submitted at the NDSS 2020 (Network and Distributed System Security Symposium).

